Digital Video Guard
Cyber attacks on government and private organisations have skyrocketed in recent times. DST Group has developed the Digital Video Guard (DVG) for protection.
How do you know whether you can trust what you are seeing on your iPad or desktop monitor? Should you really click the [YES] button? Is some software or hardware Trojan recording your password and other sensitive information?
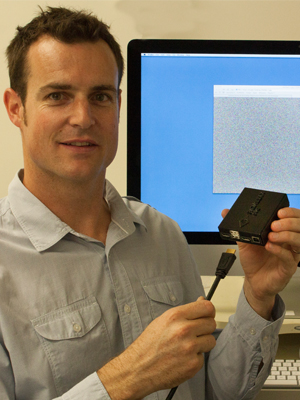
DST has developed the Digital Video Guard (DVG), a small hardware security peripheral that acts as a Hardware Trojan countermeasure.
The DVG is inserted between a host computer and a display that allows the contents of a known video signal to be trusted. If the display is decrypted and rendered successfully (i.e. it is not just garbled random pixel data) then you can be assured that the integrity and confidentiality of the data is intact.
"Because the encrypted video stream is only decrypted just before it gets to the display there is no possibility of Trojan screen grabs", says DST researcher Mark Beaumont. One of the key DVG developers, Beaumont demonstrates this easily by pressing the Print Screen button while the DVG is displaying a decrypted video window – the printed screen image shows the same window containing garbled pixel data.
Beaumont says the DVG has wide applicability for secure content delivery in areas such as internet banking and management of sensitive information such as taxation data, welfare data and medical data. “If you plug your mouse and keyboard into the DVG, it can be used to support more sophisticated functionality such as secure remote applications. The DVG can transform an untrustworthy Internet café computer into a platform suitable for remotely accessing corporate applications and email.”
Bring your own device? No problem
Science and Technology Manager Chris North believes the DVG is also the perfect option for securing data in a ‘bring your own device’ (BYOD) work environment. In BYOD workplace employees are able to bring and use their internet-enabled devices across the organisation’s network.
“It doesn’t matter how badly your kids have destroyed your tablet or laptop, because the DVG doesn’t rely on it to display the guarded video. What’s more, it is not wedded to any particular operating system, because it is decrypting the video stream between the device and the screen.”
“Using an external monitor in conjunction with a DVG, those BYOD will be able to safely access data on classified networks; all without modifying their device because our design goal is to have a zero software footprint on the user’s device,” explains Chris.
“Currently, for instance, senior government executives are issued with pared down iPads with restrictions on what they can do with them. With our DVG approach there is no restriction on the state of the user’s device. Users can do whatever they want, upgrade the operating system, let their kids install whatever apps they like, because at the end of the day the state of their machine does not affect DVG security.” North says the worst that could happen is a ‘denial of service’ attack, where the iPad basically becomes unusable.
Complex engineering
The DVG can take the form of an external device the size of a small hard drive, or be retrofitted internally. Because the DVG is decrypting video pixels ‘on the fly’ it requires some serious processing power, but the team has successfully embedded and demonstrated DVG hardware in an iPad.
The security of the DVG itself is ensured by inserting a smart card, issued by the network managers, into the device. Originally developed using proprietary encryption algorithms, the team has reduced the burden of security accreditation and the complexity and cost of implementing DVG security, by modifying it to work with existing, commercially available network routers that deploy industry standard ‘Suite B’ encryption algorithms.
Looking forward
The technology has been patented, several prototype devices are being trialled and working well and industry has been alerted to the capability in case there is interest in commercialising the product. There is potential for the technology to be used in financial, medical and messaging applications.

